We help organisations solve the security challenges that block growth, contracts, and trust.
Customers, insurers, boards, and regulators all expect documented security governance. Most organisations don't have the team or the budget to build it from scratch. Ridgeline closes that gap.
What We Solve
The security challenges that keep organisations stuck
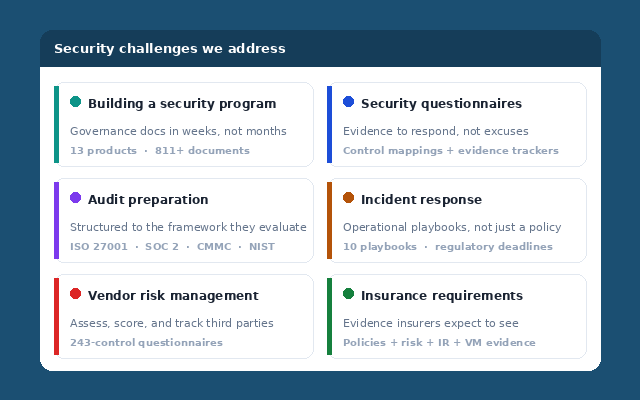
These are the situations our products and services are built to address — not theoretical risks, but the real moments where organisations need to prove their security posture.
Building a security program from zero
Your organisation has grown past the point where informal practices are enough. Customers, insurers, and auditors expect documented governance — policies, risk registers, control mappings, evidence trackers. Building this from scratch takes 6–12 months and $30,000–$100,000. Ridgeline delivers the complete documentation set in weeks.
Responding to security questionnaires and customer due diligence
A customer sends a 200-question security assessment. Without documented controls, every answer is "we're working on it" — and the deal goes to a competitor who can answer today. Our documentation gives your team evidence to respond with, not excuses.
Preparing for certification audits and regulatory assessments
ISO 27001, SOC 2, CMMC — the audit is scheduled and the documentation doesn't exist. Our toolkits are structured around the exact frameworks auditors evaluate against, with control mappings, evidence workbooks, and assessment tools already in place.
Responding to incidents without operational playbooks
Ransomware hits and your incident response plan says "follow established procedures" without defining them. GDPR gives you 72 hours to notify. Our IR toolkit gives your team attack-specific playbooks, classification engines, evidence collection scripts, and regulatory deadline tracking that work during a live incident.
Managing risk across vendors, systems, and business processes
Your risk register is an informal spreadsheet. Your vendors haven't been assessed. Your business impact analysis doesn't exist. Our risk management platform connects risk assessment, BIA, and vendor management in one system — with AI-powered analysis and board-ready reporting.
Satisfying cyber insurance requirements
Your renewal asks for documented policies, risk assessments, incident response plans, and vulnerability management evidence. Vague answers mean higher premiums or declined coverage. Our documentation provides the evidence insurers expect to see — not just a policy, but the operational proof behind it.
How Ridgeline Works
Two ways to get there — same professional outcome
Self-Deploy
Documentation Toolkits
Purchase a toolkit, customise it yourself, deploy at your pace. Complete documentation with specific parameters, framework mappings, and working Excel engines. One-time purchase — you own everything.
Browse Products →Done For You
Implementation Services
Choose any product and we customise every document to your organisation — industry, tech stack, regulatory context. Delivered in 1–2 weeks. Fixed price. You review it; your team runs it from day one.
View Services →Our Approach
What this means for your security program
Implementation-Ready, Not Theoretical
Every document contains complete content with specific parameters — 12-character password minimums, AES-256 encryption requirements, 72-hour breach notification timelines. Every Excel workbook has working formulas, conditional formatting, and sample data. Deploy it as-is or customise to your environment. No "[insert best practice here]" placeholders.
One Implementation Satisfies Multiple Audits
Every product maps to the frameworks your auditors, customers, and insurers evaluate against — NIST CSF 2.0, ISO 27001, CIS Controls, SOC 2, CMMC, PCI-DSS, GDPR. You build one security program; the framework cross-mappings handle the rest.
No Lock-In, No Dependencies
One-time purchase. Your files. Your data. Browser-based applications run locally with no server, no account, no data transmission. Export to Word, Excel, PowerPoint, JSON. If you outgrow Ridgeline, everything you've built comes with you.
Behind the Documentation
Built from implementation experience, not textbook theory
Every risk library is calibrated from real-world assessments. Every policy reflects controls that have been implemented and audited. Every framework mapping traces to specific clauses and has been verified against actual certification requirements.
The documentation contains specific parameters, realistic timelines, and practical controls — the kind of detail that only comes from doing this work in production environments across technology, financial services, professional services, defence, and healthcare.
This is not a template marketplace. Every document is built from real-world implementation and audit experience — then productised so organisations can deploy it without the consulting engagement.
811+
Documents built
5
Industry verticals covered
24+
Framework mappings
13
Products in catalogue
Security maturity isn't about perfection. It's about having the evidence that you manage risk professionally — and being able to produce it when it matters.
Get in Touch
How can we help?
Security Program Questions
Building a program, choosing a framework, evaluating which documentation fits your organisation, or questions about any of our products.
[email protected]Implementation Services
Need documentation customised to your organisation? Fixed-price implementation — any product, any framework, delivered in 1–2 weeks.
View Services →MSP & Consultant Licensing
Multi-organisation licensing, white-label options, or partnership opportunities for MSPs, consultancies, vCISOs, and resellers.
[email protected]Request Custom Documentation
Need documentation for a framework or regulation we don't currently cover? Tell us what you need.
Submit Request →