Cyber Incident Response Toolkit
36 deliverables with 4 Excel engines to operationalise your IR program — playbooks, checklists, communications templates, classification engine, and readiness scorecard.
Cyber Incident Response Toolkit
When a breach happens, you won’t have time to write a playbook.
It’s 2am. Ransomware is encrypting file shares. Your CEO’s phone is ringing. GDPR gives you 72 hours to notify. NIS2 gives you 24. DORA gives you 4. And your incident response plan is a 3-page policy that says “follow established procedures” — without defining what those procedures are.
This toolkit gives you 34 deployable deliverables — attack-specific playbooks, role-based checklists, regulatory deadline tracking, evidence collection scripts, and the Excel automation engines that run the response.
What’s inside
Respond to incidents
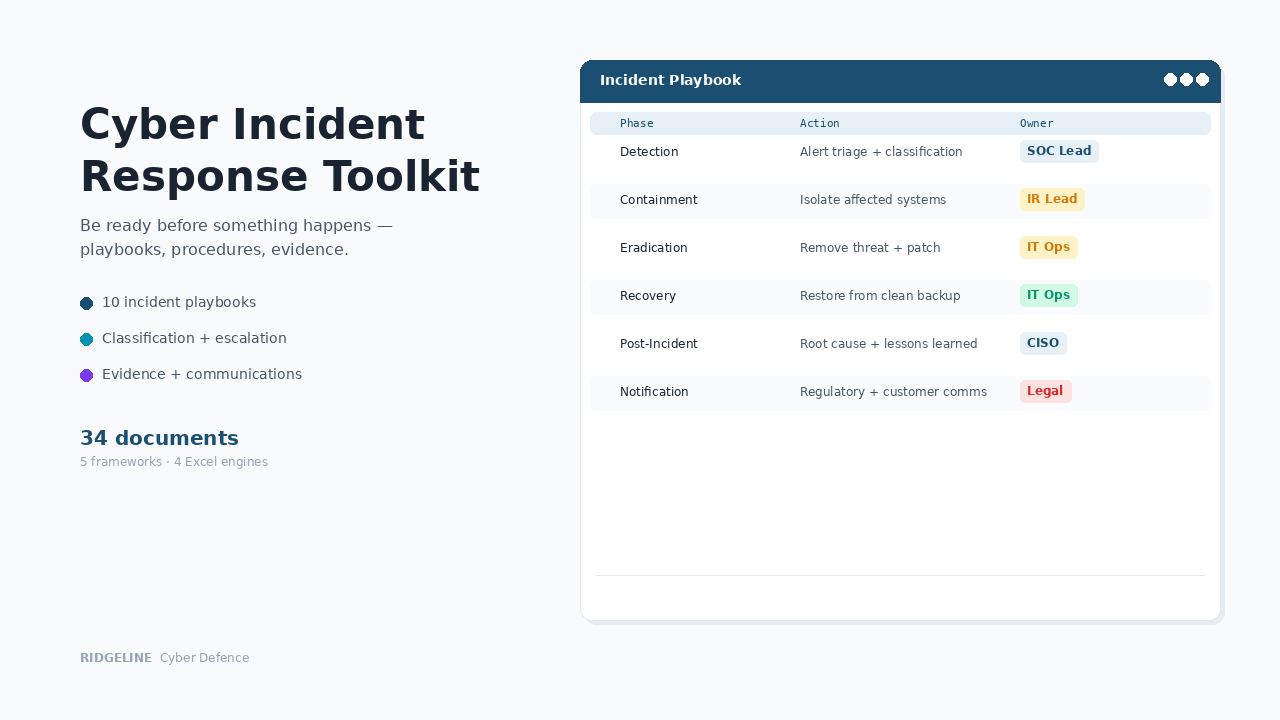
The playbooks and tools your team needs during a live incident — not theory, operational guidance.
10 Attack-Specific Playbooks
Ransomware, BEC, data breach, insider threat, DDoS, supply chain compromise, cloud compromise, web application attack, credential compromise, physical security breach.
When ransomware hits, your team opens the playbook — not a blank pageIncident Classification Engine
Excel workbook with severity auto-scoring, escalation trigger logic, regulatory deadline countdown timers with OVERDUE/URGENT status for 13 regulations.
Auto-calculates every notification deadline the moment you classifyIncident Command Workbook
9-tab real-time command centre: command log, task tracker with overdue alerting, communications log, evidence register, cost tracker, auto-generated summary.
Run the response from one workbook, not scattered emails6 Role-Specific Checklists
Phase-by-phase actions for Incident Commander, IT/Security Lead, Communications Lead, Legal/Compliance, HR, and Executive Sponsor.
Everyone knows their job — no ambiguity at 2amProtect evidence and meet deadlines
Volatile evidence disappears in minutes. Regulatory deadlines don't wait.
Evidence Preservation Guide
Volatility hierarchy, platform-specific collection commands (Windows, Linux, cloud), forensic imaging procedures, chain of custody log templates.
Evidence that survives legal scrutiny8 Evidence Collection Scripts
PowerShell and Bash scripts for Windows, Linux, memory capture, network traffic, log collection, cloud configuration, and file integrity verification.
Automated evidence collection in the right orderRegulatory Notification Reference
Deadline tracking for GDPR (72hr), NIS2 (24hr), DORA (4hr), HIPAA, PCI DSS, SEC, UK DPA — with pre-drafted notification templates.
Miss a deadline and the regulatory consequences multiplyCommunications Pack
7 pre-drafted templates: internal CMT alert, staff update, customer breach notification, regulatory filing, insurance notification, media statement, vendor notification. Approval matrix by severity.
Pre-approved language when every minute countsProve readiness and report to the board
Insurers and boards don't wait for an incident to ask about your program.
Program Readiness Scorecard
50-control maturity assessment across 10 domains with weighted scoring, insurance readiness mapping, and gap analysis linked to specific toolkit documents.
When your insurer asks about IR maturity, hand them the evidencePerformance Metrics Dashboard
200-row incident log with auto-calculated MTTD/MTTC/MTTR, RAG status against targets, quarterly trend analysis across 14 metrics, auto-populated board reports.
Board-ready metrics, not qualitative statementsGovernance Framework
IR Policy, Procedure, CMT charter, authority levels, escalation thresholds, budget governance, and maturity targets.
The governance layer every compliance audit requiresPost-Incident Review Template
Facilitation guide, 5-Whys root cause analysis, detection/response/communication effectiveness assessment, corrective actions tracker.
Turn every incident into a measurable improvementWhat these documents actually look like
The Excel engines contain 5,000+ formulas across 4 workbooks. The Classification Engine auto-calculates regulatory deadlines the moment you input severity. The Metrics Dashboard generates board reports from incident log data. Every Word document contains complete operational content — numbered steps, decision trees, and platform-specific commands.
34 deliverables that work during a live incident — not just in a filing cabinet
Playbooks · Checklists · Classification · Evidence · Notifications · Metrics · Board Reporting
When someone asks, here’s what happens
Ransomware hits at 2am
Your team opens the ransomware playbook. The Incident Commander works the command workbook. Evidence scripts capture volatile data. The Classification Engine auto-calculates every regulatory deadline. Communications templates are ready for approval.
Insurer asks about IR program maturity
You send the Program Readiness Scorecard with insurance readiness scoring across 50 controls. You don't just say "yes, we have playbooks" — you hand them the documented evidence.
Board asks for IR readiness metrics
You present the Metrics Dashboard — MTTD, MTTC, MTTR with quarterly trends, RAG status against targets, and the Readiness Scorecard trajectory. Data-driven, not qualitative.
The cost comparison
Who this is for
✓ Right fit
IT and security teams who need operational playbooks, not just a policy. Organisations preparing for ISO 27001, NIS2, or DORA. CISOs who need board-ready metrics and insurance readiness documentation.
✗ Not the right fit
Enterprises with dedicated SOC teams and established IR programs. This provides program documentation and tools — not a managed DFIR retainer. The Insurance Alignment Guide covers how to evaluate retainer providers.
Common questions
What file formats are included?
Word (.docx) for policies, procedures, playbooks, checklists, and templates. Excel (.xlsx) for the four automation engines. PowerShell and Bash scripts for evidence collection. All files use standard fonts and formatting.
Do I need to buy other Ridgeline products first?
No. The toolkit is self-contained with its own IR policy, procedure, and governance framework. If you already own the Information Security Policy Suite, the IR Policy in this toolkit supersedes POL-005.
Does this replace a managed IR retainer?
No. This provides program documentation and operational tools. You still need technical response capability — whether in-house, through a DFIR retainer, or both. The Insurance Alignment Guide covers how to evaluate and select retainer providers.
What regulatory notification deadlines are covered?
GDPR (72 hours), NIS2 (24 hours), DORA (4 hours), HIPAA (60 hours), PCI DSS (72 hours), SEC (96 hours), UK DPA (72 hours), plus custom slots. The Classification Engine auto-calculates deadlines the moment you classify an incident.
How long does implementation take?
Core documents (policy, procedure, classification engine, checklists) deploy within a day. Full program operationalisation — including training, tabletop exercises, and metrics baseline — typically takes 2–4 weeks.
Do I get updates if the product is improved?
Yes. If we update this product within 12 months of your purchase — framework changes, new templates, content improvements — you receive the updated files automatically at no additional cost. After 12 months, you keep everything you have permanently. Future updates are available at a renewal discount.
Is AI used in creating these documents?
Ridgeline uses AI tools in the research and drafting process. All documentation is written, reviewed, and validated by a security practitioner to ensure it is operationally sound and aligned with current frameworks.
What if we need help customising it?
Our Implementation Services team will customise playbooks, configure the classification engine, and tailor communications templates to your organisation. Toolkit tier is $2,997, delivered in 1–2 weeks.
How does this compare?
| Capability | Free templates | Cyber Incident Response Toolkit | GRC platform ($15K+/yr) |
|---|---|---|---|
| Framework-aligned documentation | Some | ✓ Full coverage | ✓ |
| Editable Word/Excel files | ✓ | ✓ | ✗ Locked in platform |
| Interactive browser app | ✗ | ✗ | ✓ |
| One-time cost | ✓ Free | ✓ $797 | ✗ Annual subscription |
| Implementation time | Weeks | ✓ Hours | Months |
| Audit-ready formatting | ✗ Inconsistent | ✓ Professional | ✓ |
Get notified about updates to this toolkit
Get notified when we launch new toolkits
Product launches only · No spam · Unsubscribe anytime
Implementation Services
Need this customised to your organisation?
We'll customise any product to your organisation and deliver in 1–2 weeks. Fixed price, fully async. You review it, your team runs it.
Foundation $1,997 · Toolkit $2,997 · Suite $5,997 · Program $8,997