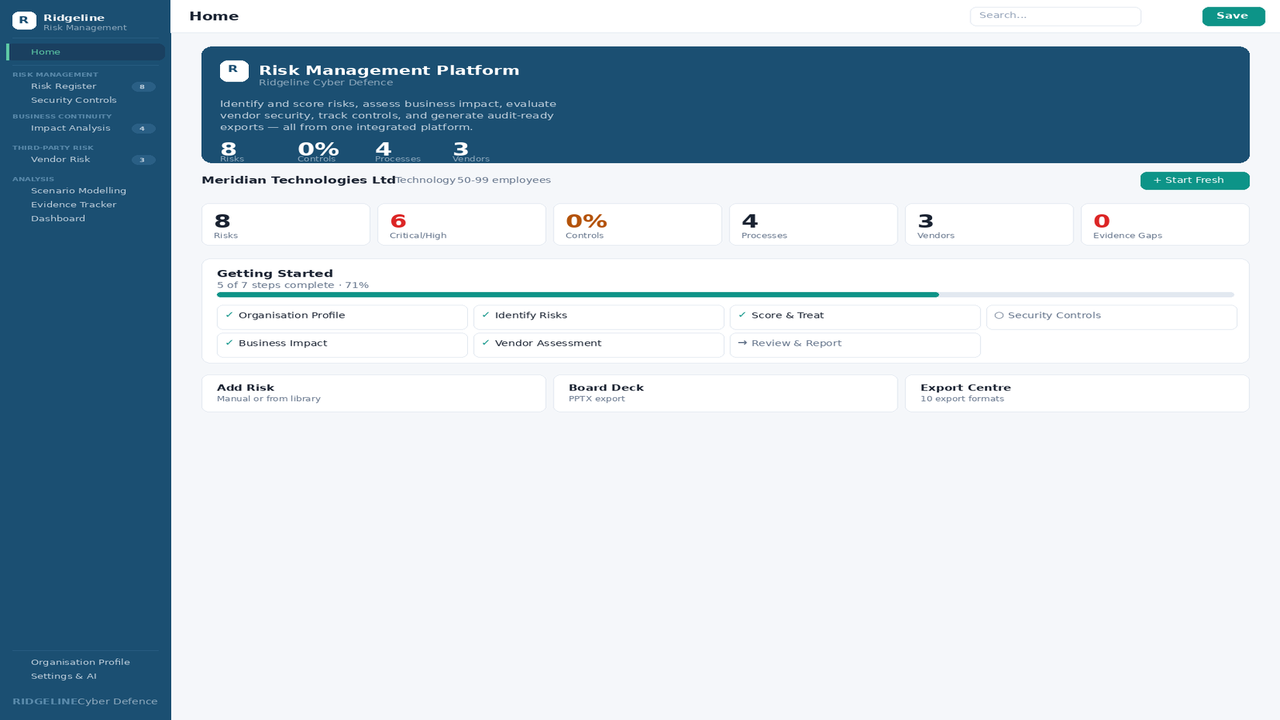
Security Program Foundation Toolkit
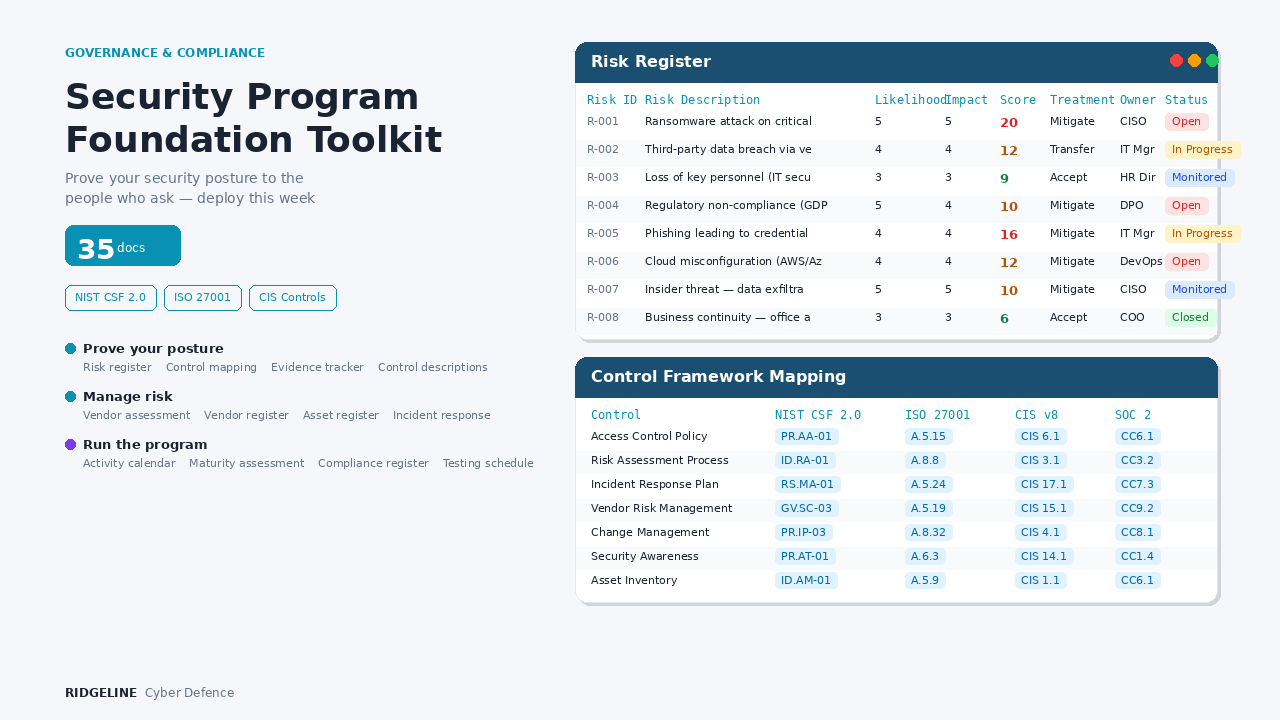
35 documents to build and prove a documented security program — risk register, control mappings, evidence trackers, vendor management, and maturity assessment.
Security Program Foundation Toolkit
Someone is going to ask about your security program. Be ready.
A customer sends a questionnaire. An insurer asks for controls. A board member asks for metrics. An auditor asks for evidence. The question isn’t if — it’s when.
This toolkit gives you the 35 documents they actually ask for. Risk registers, control mappings, evidence trackers, vendor assessments, and the governance calendar that keeps it all current. Customise them to your organisation, and the next time someone asks, you open a folder and send what they need.
What’s inside
Prove your security posture
The four documents customers and auditors ask for first.
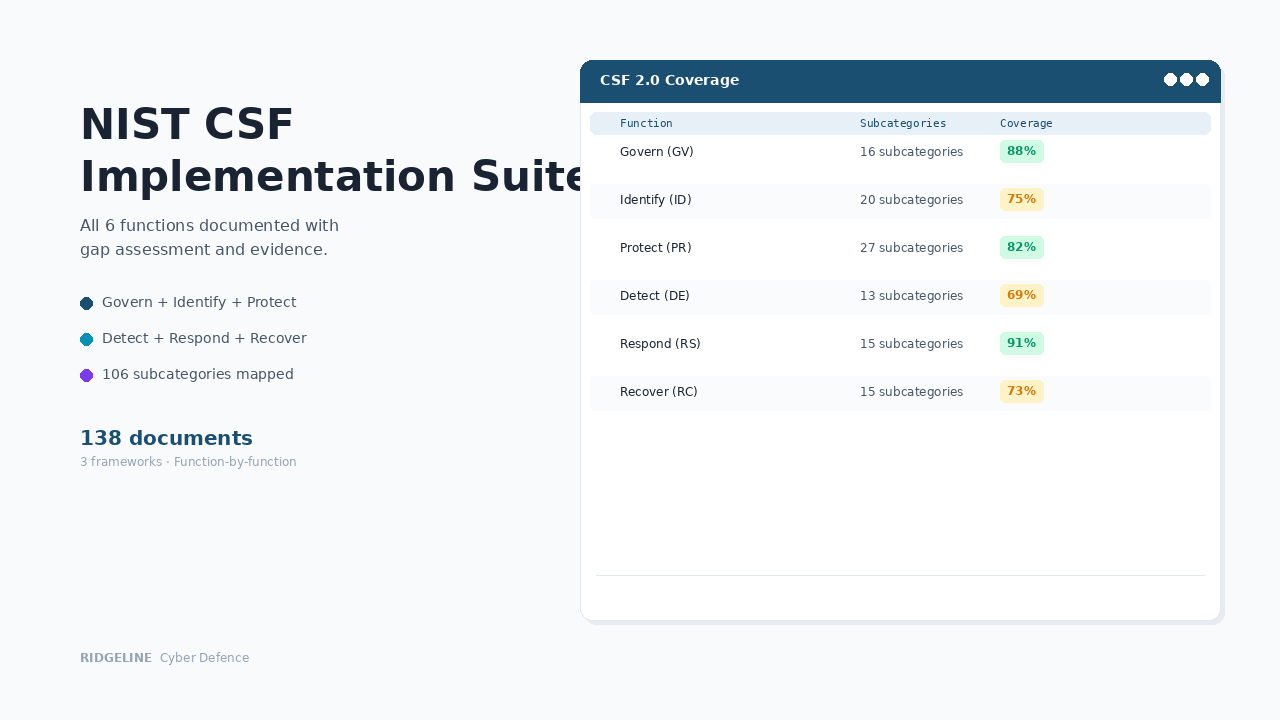
Risk Register
5×5 matrix with scoring, treatment plans, owners, and review dates. Pre-loaded with sample risks.
First thing every auditor asks forControl Framework Mapping
Maps your controls to NIST CSF 2.0, ISO 27001, CIS v8, and SOC 2. Traces to specific clauses.
Answer "which framework do you follow?"Evidence Collection Tracker
Every piece of evidence catalogued by control — what you have, where it's stored, what's missing.
Produce evidence in minutes, not daysControl Descriptions
What each control does, who owns it, how it's tested, which framework requirements it satisfies.
From "yes we do that" to proofManage risk and vendors
What insurers and enterprise procurement teams check next.
Third-Party Risk Assessment
33-question vendor security questionnaire covering data handling, access controls, IR, and continuity.
Your vendors are your attack surfaceVendor Register
Central inventory with risk tiers, contract dates, data access classifications, and review schedules.
"Which vendors have customer data?" — 30 secondsAsset Register
Hardware, software, and data inventory with classification levels, owners, and locations.
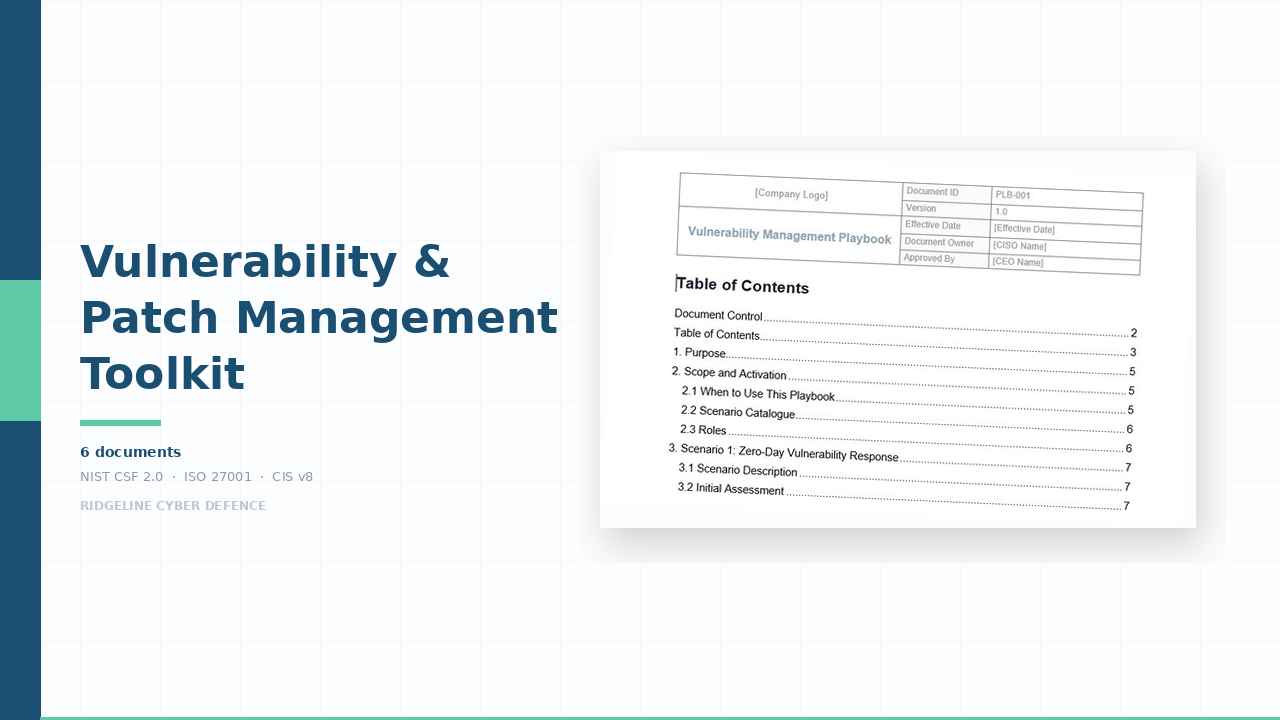
Can't protect what you haven't inventoriedIncident Response Plan
Severity classification (S1–S4), escalation paths, communication templates, post-incident review.
Insurers and customers both require thisKeep the program running
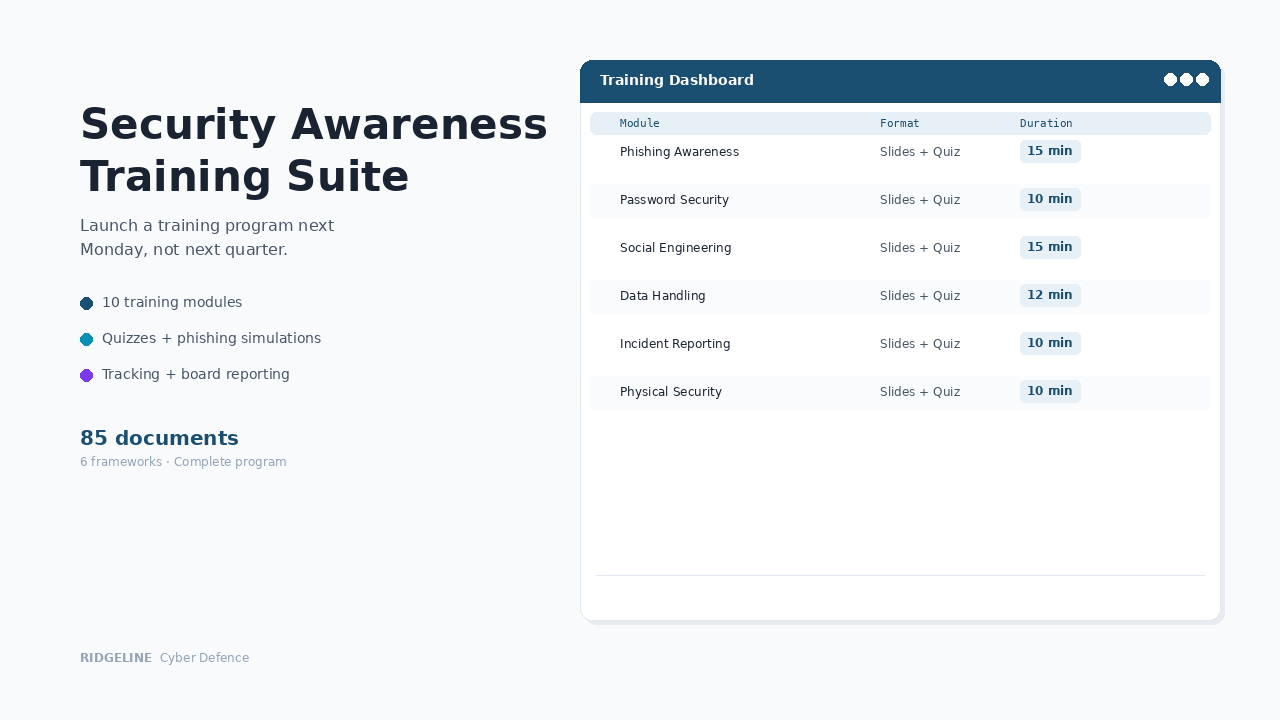
Security programs fail when they're treated as a one-time project. These keep it operational.
GRC Activity Calendar
30 activities across 12 months — risk reviews, control testing, vendor assessments, policy reviews.
Governance becomes routine, not a scrambleMaturity Assessment
30-question self-assessment across 7 domains with scoring and maturity level definitions.
Measure day one, show progress at month sixCompliance Obligations Register
Every regulatory requirement, contractual obligation, and framework commitment with deadlines.
Never miss a compliance deadlineControl Testing Schedule
Quarterly testing with pass/fail criteria, evidence requirements, and remediation tracking.
Prove controls work, not just existWhat these documents actually look like
Every Excel workbook includes data validation dropdowns, conditional formatting that highlights what needs attention, dashboard views with live calculations, and sample data showing realistic examples. The Word documents contain complete content with specific parameters — not “insert best practice here” placeholders.
Same 35 documents handle all four situations
Customers · Insurers · Boards · Investors
When someone asks, here’s what happens
Customer sends a security questionnaire
You pull the risk register, control framework mapping, and evidence tracker. Respond within 48 hours with documented evidence. No follow-up questions.
Insurer asks for evidence at renewal
You attach the incident response plan, risk register, and vendor register. Application completed in an afternoon — not three weeks of guesswork.
Board asks about security posture
You present the maturity assessment and risk register data. Evidence-based answer with actual metrics — not "we're working on it."
Investor asks about security during due diligence
You show the maturity score, control framework mapping, and risk register. Demonstrates professional governance — the kind that closes rounds, not delays them.
The cost comparison
Who this is for
✓ Right fit
20–200 person companies that need to demonstrate security maturity to customers, insurers, boards, or regulators — and don't have a dedicated GRC team to build it from scratch.
✗ Not the right fit
Enterprises with dedicated compliance teams and six-figure budgets. Companies that already have mature documentation. Anyone expecting compliance without doing any of the work.
Common questions
We're a 30-person company. Is 35 documents overkill?
No. A 30-person company gets the same security questionnaire as a 3,000-person company. The frameworks don't scale down based on headcount. These 35 documents are specifically the ones that questionnaires, auditors, and insurers ask for — nothing in here exists to pad the count.
What format are the files?
Excel (.xlsx) for registers, trackers, and assessments. Word (.docx) for plans and procedures. Works in Microsoft 365, Google Workspace, or LibreOffice.
How long until we can respond to a questionnaire?
Most companies start with the Risk Register and Control Framework Mapping — the two documents requested most frequently — and have them customised within a few days. The implementation guide tells you what to do first.
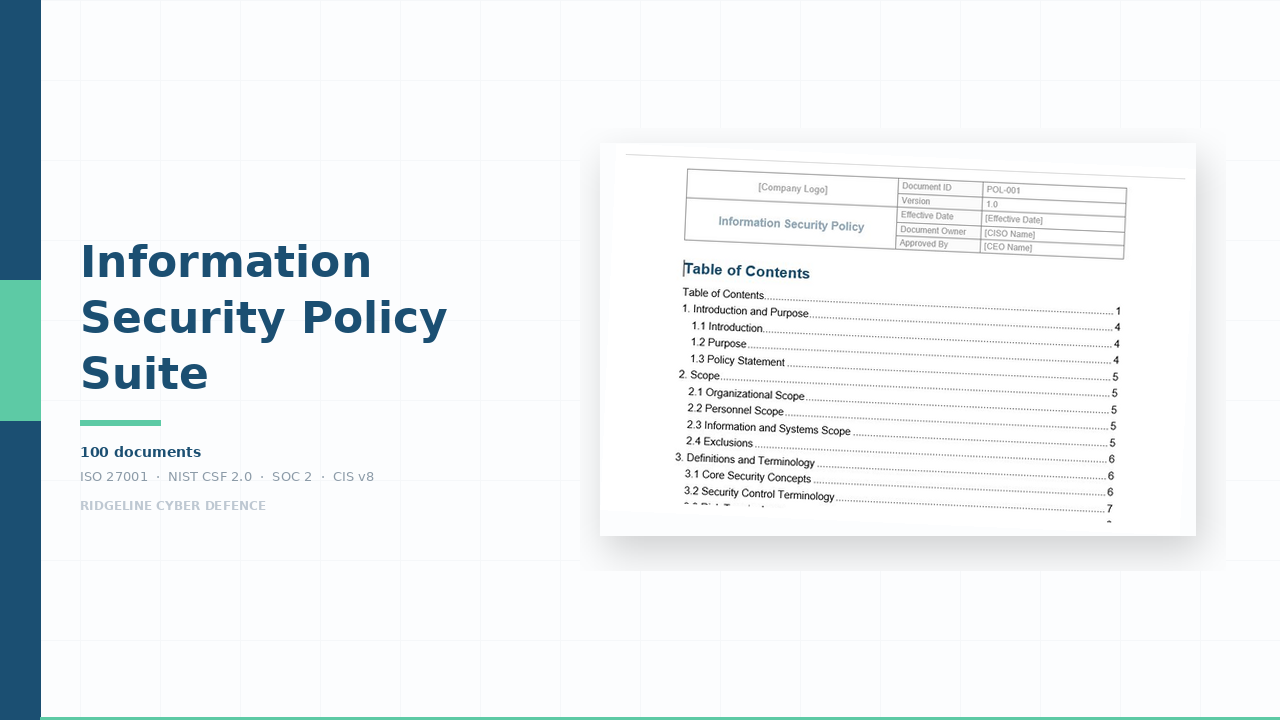
Don't we need policies too?
Policies are the "what we commit to doing" layer. This toolkit is the "proof that we're doing it" layer. A completed risk register and control mapping is more useful to an auditor than a policy with no evidence behind it. When you're ready, the Information Security Policy Suite pairs directly with this toolkit.
We don't understand frameworks. Can we still use this?
Yes. The Control Framework Mapping does the translation — it shows which of your controls satisfy which requirements across NIST, ISO, CIS, and SOC 2. You fill in what you're doing; the mapping tells you where you stand.
Will this get us through a SOC 2 audit?
It gives you the documentation foundation. SOC 2 also requires a CPA firm audit and evidence of controls operating over time. If SOC 2 is your primary goal, the SOC 2 Readiness Suite has the complete documentation set.
Do I get updates if the product is improved?
Yes. If we update this product within 12 months of your purchase — framework changes, new templates, content improvements — you receive the updated files automatically at no additional cost. After 12 months, you keep everything you have permanently. Future updates are available at a renewal discount.
Is AI used in creating these documents?
Ridgeline uses AI tools in the research and drafting process. All documentation is written, reviewed, and validated by a security practitioner to ensure it is operationally sound and aligned with current frameworks.
What if we need help customising it?
Our Implementation Services team will customise it to your organisation — industry, tech stack, regulatory requirements. Toolkit tier is $2,997, delivered in 1–2 weeks.
How does this compare?
| Capability | Free templates | Security Program Foundation Toolkit | GRC platform ($15K+/yr) |
|---|---|---|---|
| Framework-aligned documentation | Some | ✓ Full coverage | ✓ |
| Editable Word/Excel files | ✓ | ✓ | ✗ Locked in platform |
| Interactive browser app | ✗ | ✗ | ✓ |
| One-time cost | ✓ Free | ✓ $497 | ✗ Annual subscription |
| Implementation time | Weeks | ✓ Hours | Months |
| Audit-ready formatting | ✗ Inconsistent | ✓ Professional | ✓ |
Get notified about updates to this toolkit
Get notified when we launch new toolkits
Product launches only · No spam · Unsubscribe anytime
Implementation Services
Need this customised to your organisation?
We'll customise any product to your organisation and deliver in 1–2 weeks. Fixed price, fully async. You review it, your team runs it.
Foundation $1,997 · Toolkit $2,997 · Suite $5,997 · Program $8,997