Information Security Policy Suite
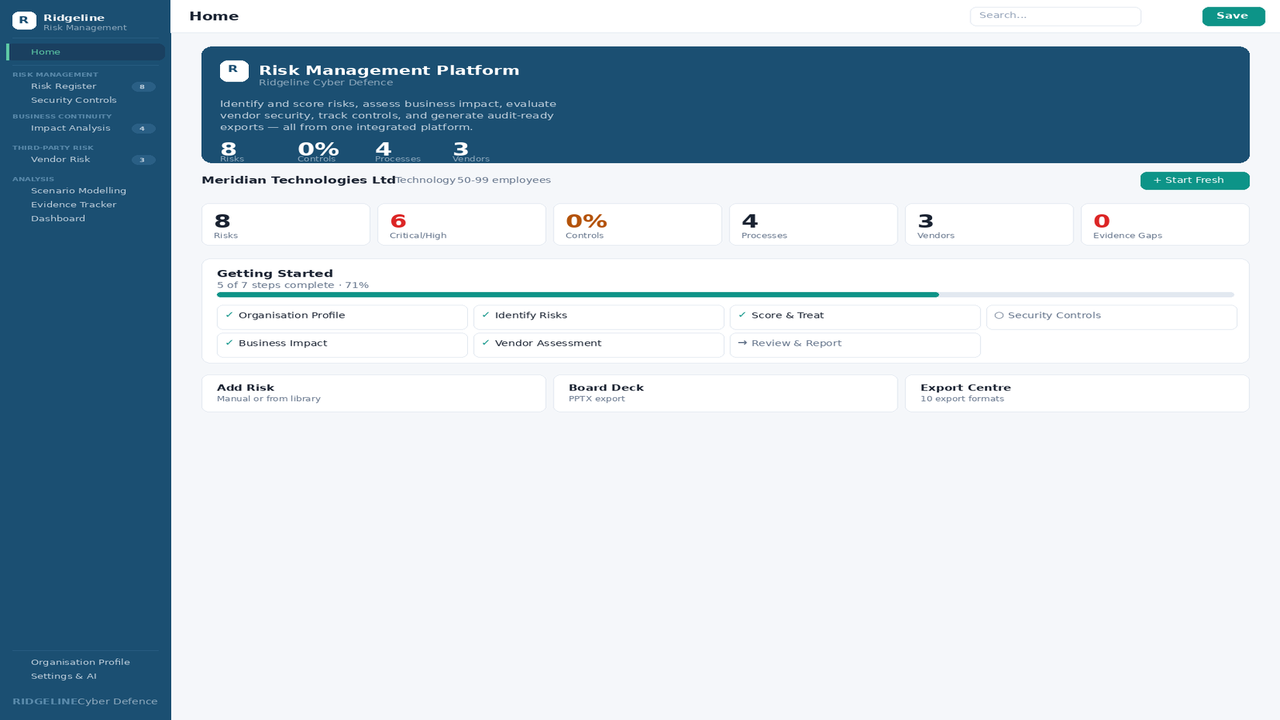
Desktop ISMS application with 100 documents, 93-control compliance assessment, policy acknowledgment tracking, questionnaire response generator, traceability matrix, board reporting, and 6 AI providers. The complete information security management system in one installed application.
Information Security Policy Suite
Your auditor wants an ISMS. Your board wants visibility. Your customer wants proof.
An ISMS isn’t a single policy — it’s the interconnected set of policies, standards, processes, procedures, and forms that govern how your organisation protects information. Plus the management system that tracks compliance, manages lifecycle, identifies gaps, and reports to the board. Building this from scratch takes a GRC analyst 6–12 months. A GRC platform costs $10,000–$50,000/year with lock-in.
This suite gives you 100 documents and a desktop application to run them — for a one-time cost, with zero cloud dependency.
What’s inside
Prove your security posture
The documents and tools auditors, customers, and boards ask for first.
21 Security Policies
Board-level governance: information security, access control, incident response, data protection, business continuity, risk management, and 15 more. Complete content — not "insert best practice here."
The foundation every auditor evaluates firstCompliance Assessment Engine
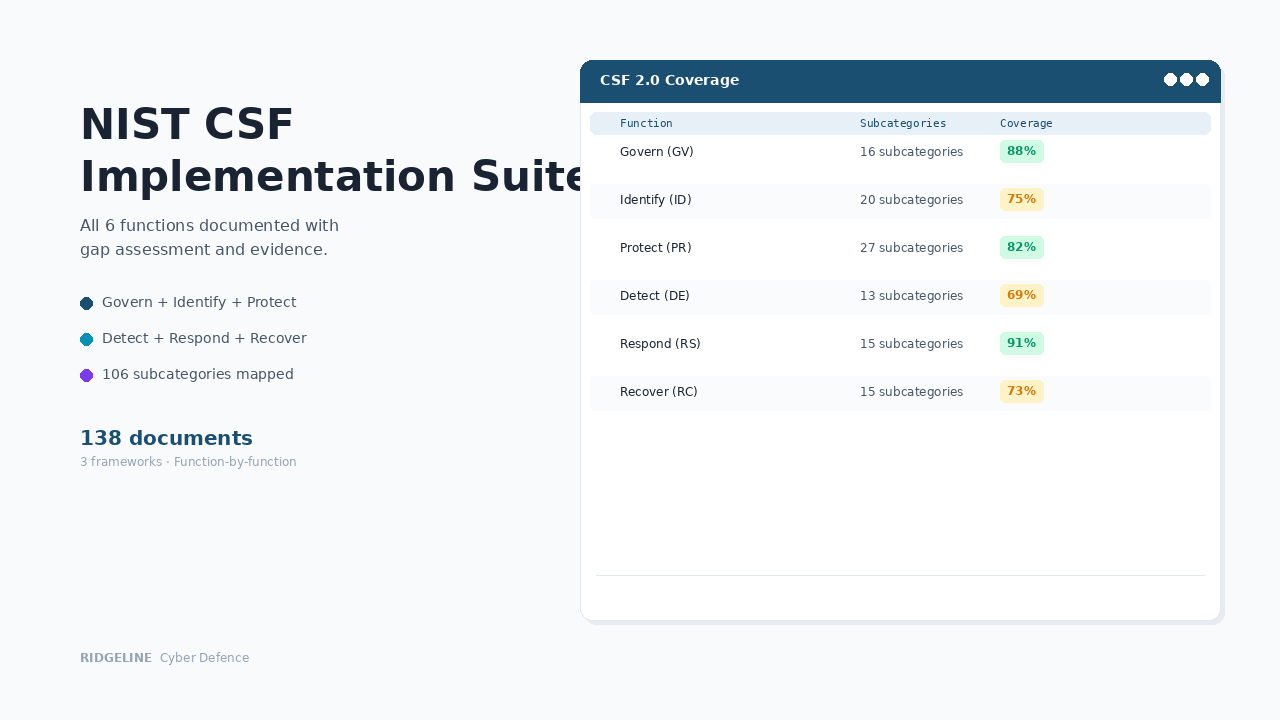
Score against 93 ISO 27001:2022 Annex A controls with NIST CSF 2.0 and CIS Controls v8 cross-mappings. Risk-prioritised gaps with remediation guidance that links each gap to a specific action and document.
Know exactly where you stand — and what to do about each gapControl-to-Policy Traceability Matrix
Clickable matrix mapping every ISO 27001, NIST CSF, CIS, and SOC 2 control to the specific policy section that addresses it. Auditors evaluate traceability — this shows it in one view.
Show auditors exactly which policy addresses each control requirementEvidence Tracker
Map evidence artefacts to specific controls. Collection status by domain, owner assignment, deadline tracking, and automatic gap identification across risks, controls, and policies.
Produce evidence in minutes, not daysOperate the program
The operational layer that turns policies into daily practice.
15 Technical Standards
Specific parameters: 12-character password minimums, MFA tiers, AES-256 encryption, TLS 1.2+, endpoint hardening, cloud configuration, and 9 more.
Policies say "what" — standards say "how much"12 Operational Processes
Risk assessment, incident response, change management, vulnerability management, vendor assessment, internal audit, and 6 more workflow definitions.
Repeatable workflows that survive staff turnover28 Step-by-Step Procedures
Firewall changes, certificate management, DR testing, phishing simulations, supplier assessments, management reviews — numbered steps, responsible parties, verification criteria.
Anyone on the team can execute, not just the person who set it up22 Forms & Trackers
Access requests, incident reports, change requests, risk assessments, vendor assessments, security metrics dashboards — with formulas, conditional formatting, and dropdowns pre-configured.
Capture evidence as you work, not after the factManage the lifecycle
Security programs fail when policies expire and nobody notices. These keep it current.
Policy Lifecycle Management
Track every document from Draft through Approved to Expired. Automated review reminders, version comparison with diffs, owner and approver assignment, bulk updates for annual review cycles. Calendar view of upcoming reviews.
"When was this last reviewed?" — instant answerPolicy Acknowledgment Tracking
Register which employees have read and accepted each policy. Track acknowledgment campaigns, flag employees who need to re-acknowledge after policy updates, and export the register for auditors.
Prove to auditors that your people have read the policiesQuestionnaire Response Generator
100 pre-loaded security questionnaire questions with response templates mapped to your policies. Paste a question, get a response with policy references and evidence links. AI-assisted drafting for custom questions.
Answer security questionnaires in hours, not weeksBoard Reporting Pack
One-click generation of a board-ready report: compliance posture, policy review status, evidence gaps, acknowledgment status, upcoming actions. PPTX and PDF output with your branding.
Quarterly board reporting in one click, not a manual buildProfessional desktop application
Not a browser file — a proper installable application with encrypted storage and AI integration.
Desktop Application
Native Windows application with installer. Sidebar navigation, global search, command palette, light theme with brand headers. Browse, search, and navigate all 100 documents inside the app.
Opens like any desktop app — professional, fast, offlineAI-Powered Analysis
BYOK integration with 6 providers — Claude, ChatGPT, Gemini, Grok, DeepSeek, and local LLMs. Dynamic model selection. AI assists gap remediation, questionnaire responses, audit preparation, and board reporting.
AI that uses your API key on your machine — no data leaves your deviceEncrypted Local Storage
All data stored locally in SQLite. API keys secured via OS keychain (Windows Credential Manager). No cloud, no server, no data transmission.
Your compliance data never leaves your machineImplementation Wizard & Audit Simulator
Phased deployment plan based on your profile. Audit simulator tests your readiness with domain-based questions. Remediation tracker with effort estimates, priorities, and quick-win identification.
Deploy in weeks — and find the gaps before your auditor does100 documents + the desktop application to run them
$1,497 · One-time purchase · Desktop application · No data leaves your device · 12 months of updates
When someone asks, here’s what happens
Customer sends a security questionnaire
You open the Questionnaire Response Generator, paste their questions, and get policy-referenced responses with evidence links. AI drafts custom answers. Response sent within 48 hours, not weeks.
Auditor asks to see your ISMS
You show them the Traceability Matrix with 93 controls mapped to specific policy sections, the Policy Lifecycle with review dates and version history, and the Evidence Tracker with artefacts linked to controls. Structured around the framework they evaluate.
Board asks about security posture
You click "Generate Board Report" — compliance posture, policy review status, acknowledgment completion, evidence gaps, upcoming actions. One-click PPTX export. Evidence-based answer with actual data.
Policy is updated — who needs to re-acknowledge?
The Acknowledgment Tracker automatically flags every employee who accepted the previous version. Version comparison shows exactly what changed. Campaign creator notifies the right people.
The cost comparison
Who this is for
✓ Right fit
Organisations building or maturing an ISMS — whether pursuing ISO 27001, responding to customer questionnaires, or getting cyber insurance. Security managers who need one system for policies, compliance, evidence, and reporting without a six-figure platform budget.
✗ Not the right fit
Enterprises with existing GRC platforms and dedicated compliance teams. Organisations that only need a basic set of governance documents without the management application — the Security Program Foundation Toolkit covers that at $497.
Common questions
Is this a desktop application or a browser app?
Desktop application. You download and install it like any software. It runs natively on Windows with no browser required. All data is stored locally on your machine — nothing is transmitted to any server.
How is this different from buying policy templates?
Template products give you static Word files. This includes all 100 documents plus a desktop application with a Policy Content Engine, Compliance Assessment, Traceability Matrix, Policy Lifecycle with version diffs, Acknowledgment Tracking, Questionnaire Response Generator, Evidence Tracker, Board Reporting, and Dashboard. You get the documents and the system to manage them.
Which AI providers are supported?
Six providers: Anthropic (Claude), OpenAI (ChatGPT), Google (Gemini), xAI (Grok), DeepSeek, and local LLMs (Ollama, LM Studio, or any OpenAI-compatible endpoint). You bring your own API key — it's stored encrypted in your OS keychain. The app dynamically fetches available models from your provider. AI is optional — every feature works without it.
Can I use this for ISO 27001 certification?
Yes. Covers all 93 ISO 27001:2022 Annex A controls with the Traceability Matrix linking each control to specific policy sections. The Compliance Assessment identifies gaps, the Remediation Tracker prioritises fixes with effort estimates, and the Audit Simulator prepares your team for the certification audit.
How does the Questionnaire Response Generator work?
100 pre-loaded security questionnaire questions with response templates in three variants (short, standard, detailed). Each response references specific policies and evidence. Paste a custom question and the app matches it to relevant policies — or use AI to draft a response. Export the complete questionnaire as XLSX or DOCX.
We already have some policies. Do we need all 100 documents?
The Compliance Assessment will show exactly which controls your existing policies cover and where gaps remain. The Remediation Tracker identifies quick wins — gaps you can close immediately by deploying existing toolkit documents. Most organisations have policies but lack the standards, procedures, forms, and the management system that tracks everything.
Is my data secure?
All data is stored locally in an encrypted SQLite database on your machine. API keys are stored in your OS keychain (Windows Credential Manager). No data is transmitted to any server — AI calls go directly from your machine to your chosen provider using your own API key.
Do I get updates if the product is improved?
Yes. If we update this product within 12 months of your purchase — framework changes, new features, content improvements — you receive the updated version automatically at no additional cost. After 12 months, you keep everything you have permanently. Future updates are available at a renewal discount.
Is AI used in creating these documents?
Ridgeline uses AI tools in the research and drafting process. All documentation is written, reviewed, and validated by a security practitioner to ensure it is operationally sound and aligned with current frameworks.
What if we need help customising it?
Our Implementation Services team will configure the application with your data and customise all documents to your organisation — industry, tech stack, regulatory requirements. Suite tier is $5,997, delivered in 1–2 weeks.
How does this compare?
| Capability | Free templates | Information Security Policy Suite | GRC platform ($15K+/yr) |
|---|---|---|---|
| Framework-aligned documentation | Some | ✓ Full coverage | ✓ |
| Editable Word/Excel files | ✓ | ✓ | ✗ Locked in platform |
| Interactive browser app | ✗ | ✓ Included | ✓ |
| One-time cost | ✓ Free | ✓ $1,497 | ✗ Annual subscription |
| Implementation time | Weeks | ✓ Hours | Months |
| Audit-ready formatting | ✗ Inconsistent | ✓ Professional | ✓ |
Get notified about updates to this toolkit
Get notified when we launch new toolkits
Product launches only · No spam · Unsubscribe anytime
Implementation Services
Need this customised to your organisation?
We'll customise any product to your organisation and deliver in 1–2 weeks. Fixed price, fully async. You review it, your team runs it.
Foundation $1,997 · Toolkit $2,997 · Suite $5,997 · Program $8,997