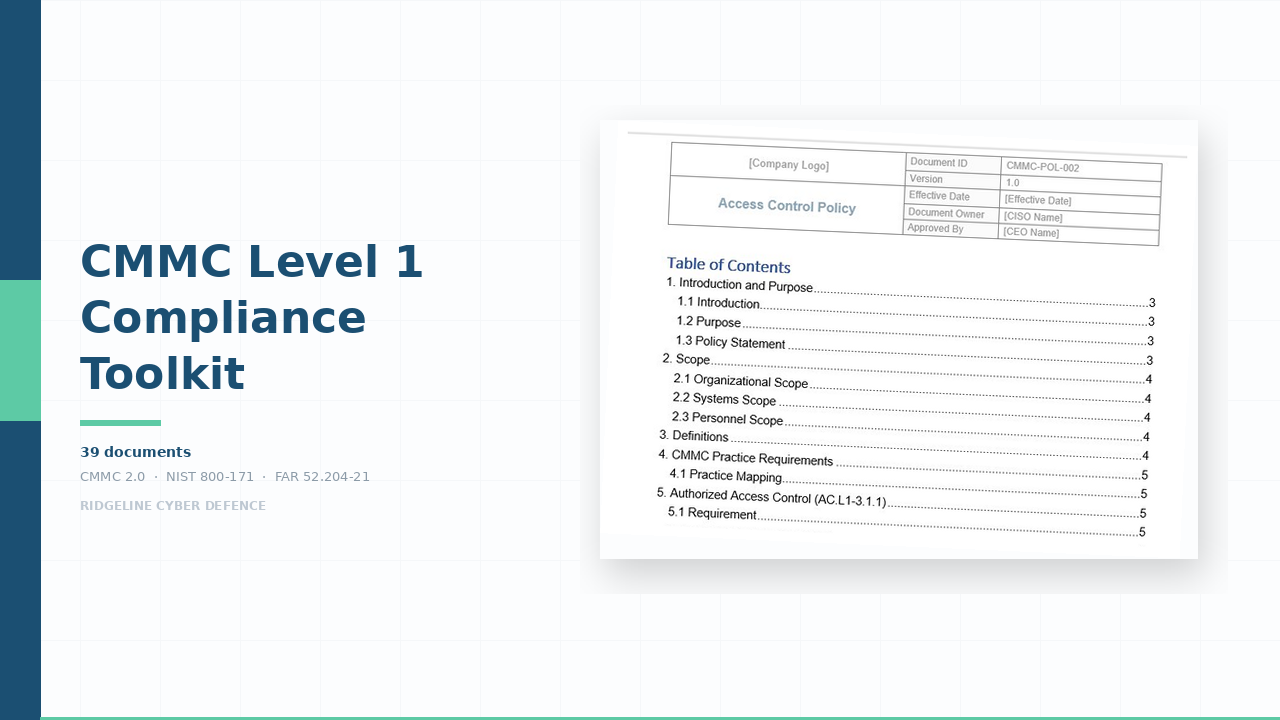
SOC 2 Readiness Suite
Complete SOC 2 audit documentation — policies, procedures, system description, control matrix, and evidence workbooks mapped to AICPA Trust Services Criteria.
SOC 2 Readiness Suite
Your customer just asked for SOC 2. The deal depends on your answer.
Enterprise customers won’t sign without it. Investors expect it during due diligence. Cyber insurers ask about it. The documentation requirement is substantial — system descriptions, control narratives, policies, procedures, evidence workbooks, and control matrices structured around AICPA Trust Services Criteria. Building this from scratch takes 3–6 months. Hiring a consultant costs $15,000–$50,000.
This suite gives you 69 audit-ready documents structured around the exact framework your auditor evaluates — customise for your environment in weeks, not months.
What’s inside
Prove SOC 2 readiness
The documents your auditor evaluates first — and the ones that take longest to create from scratch.
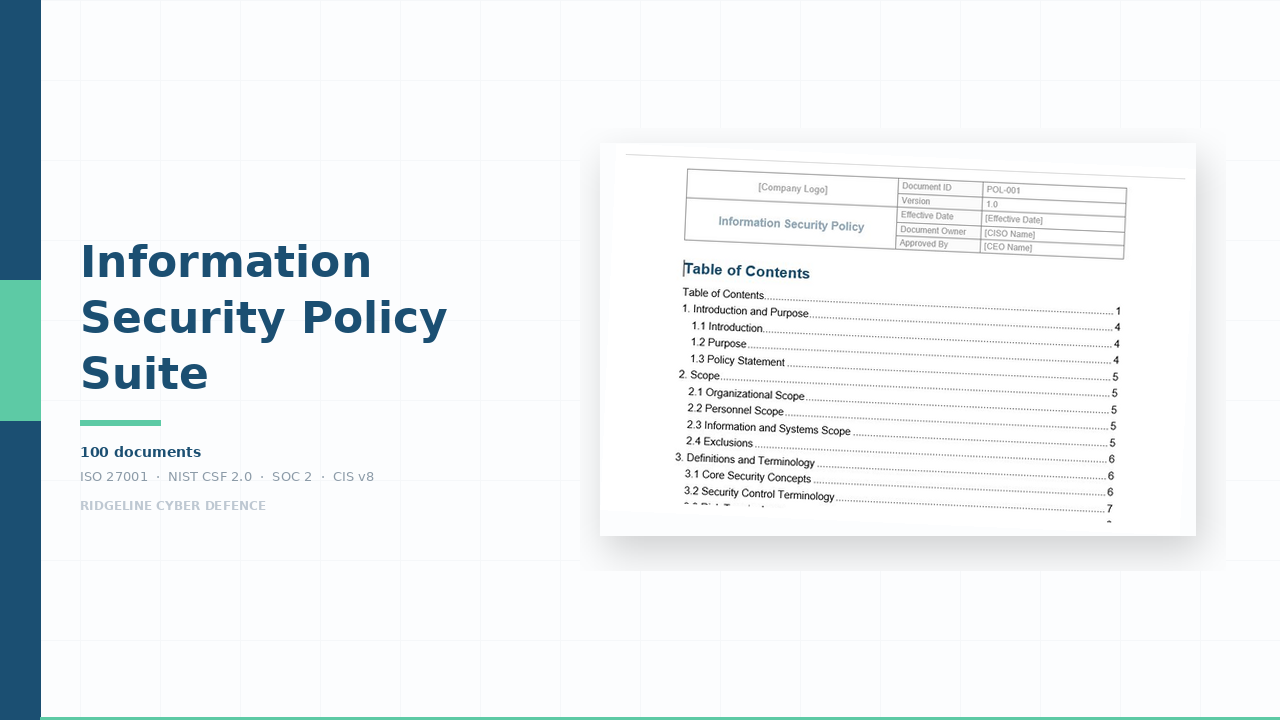
System Description Template
Complete AICPA structure: principal service commitments, system components, boundaries, subservice organisations, complementary controls. 12+ sections with guidance notes.
The core of your SOC 2 report — most companies have never written one30+ Control Narratives
Pre-written in the language auditors expect. Each describes the control objective, activity, how it operates, frequency, and responsible party.
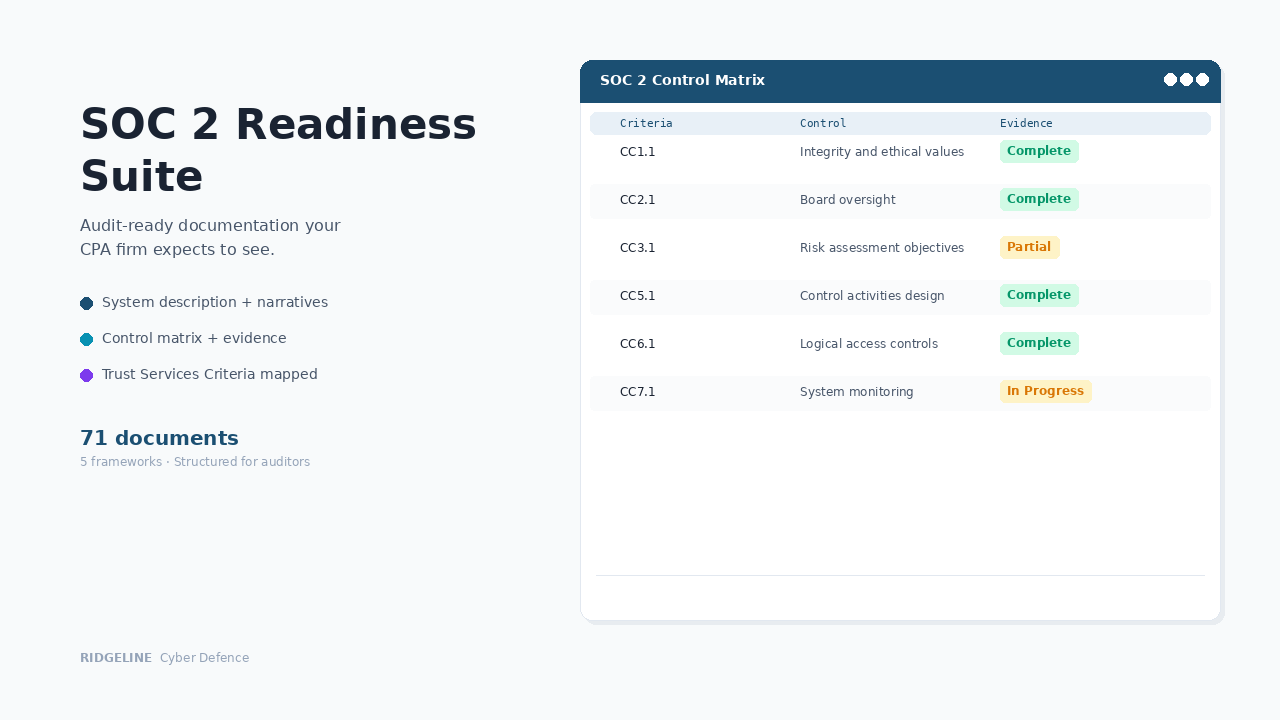
The part that takes weeks to draft — doneSOC 2 Control Matrix
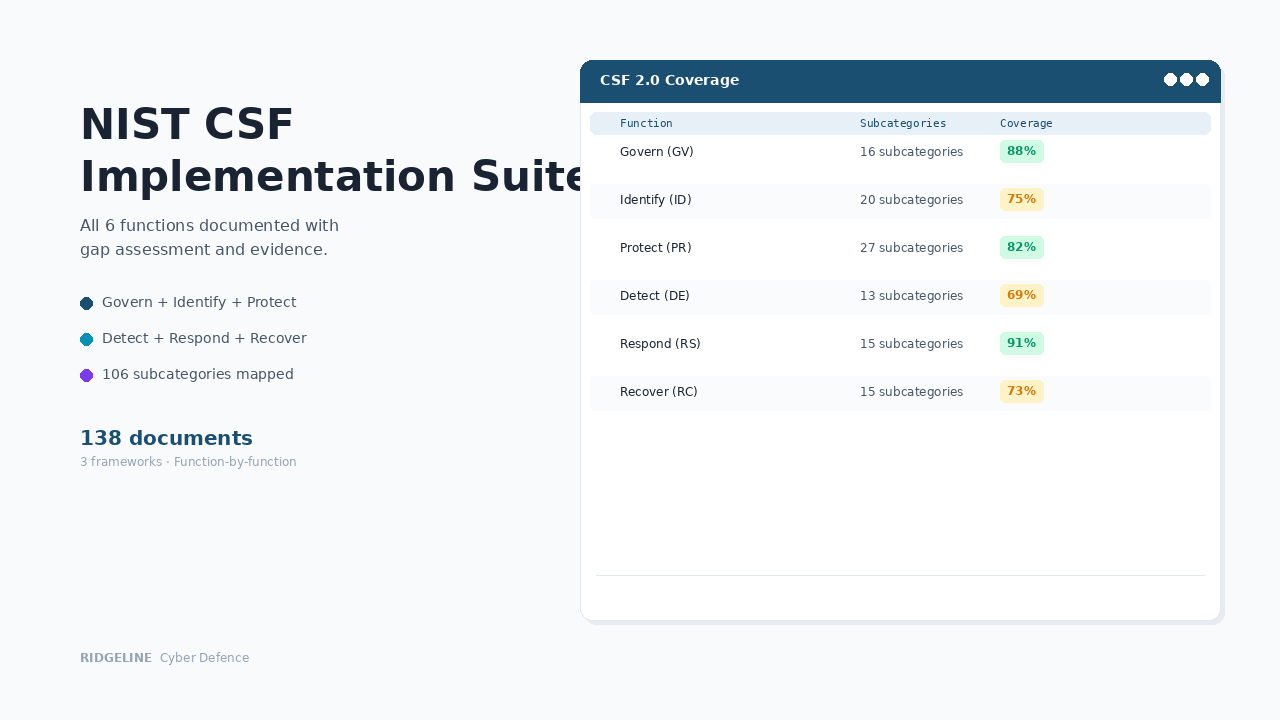
Complete CC1–CC9 mapping with control objectives, activities, owners, testing frequency, and evidence requirements. TSC-to-Framework crosswalk for NIST CSF 2.0, ISO 27001, and CIS v8.
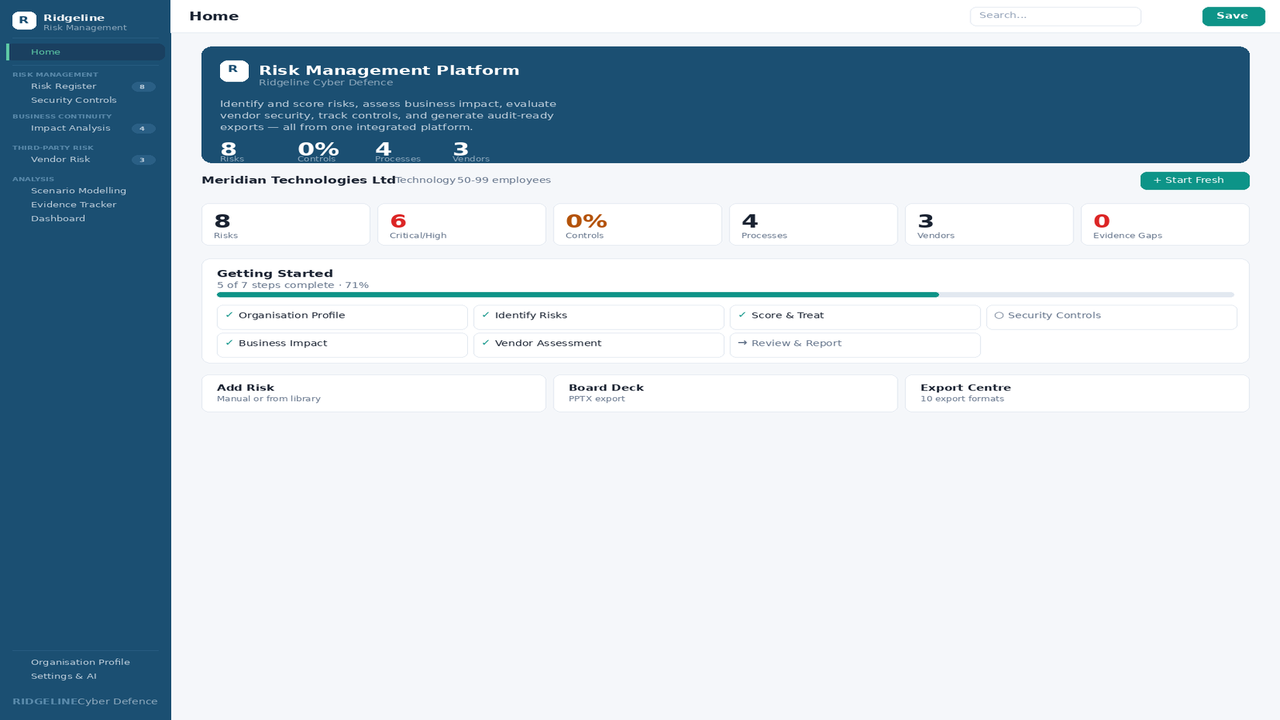
One implementation satisfies multiple audits simultaneouslySOC 2 Readiness Assessment
Self-assessment against all CC1–CC9 criteria with scoring, gap identification, and remediation priorities.
Know exactly where you stand before the auditor arrivesCollect and track evidence
SOC 2 Type II requires evidence that controls operate over time — not just that they exist.
Evidence Collection Workbook
41 evidence items mapped to specific controls with dropdown-validated fields. Your team knows exactly what to gather before the auditor arrives.
No more guessing what "sufficient evidence" looks likeControl Testing Workbook
50 test rows with summary dashboard and 55 formulas. 4-step testing methodology with sampling guidance for internal audit.
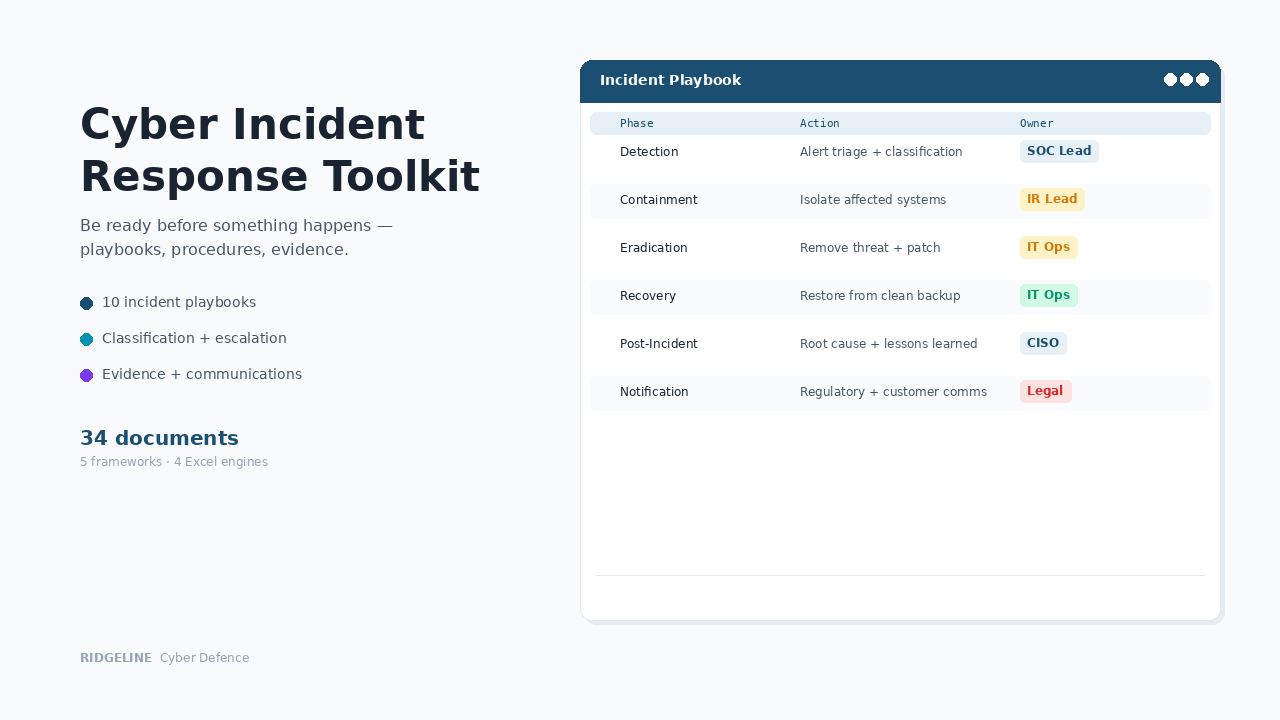
Prove controls work, not just exist on paper14 Security Policies
Information security, access control, change management, incident response, risk management, encryption, network security, vendor risk, business continuity, and 5 more. Each maps directly to specific CC criteria.
The policy foundation your controls are built on10 Operational Procedures
User access provisioning, access reviews, change management, incident response, risk assessment, vendor assessment, vulnerability scanning, monitoring, onboarding/offboarding, backup testing.
Step-by-step processes your team can execute consistentlyPrepare for the audit
Professional tier adds full Trust Service Category coverage and auditor preparation materials.
Auditor Preparation Package
Pre-Audit Preparation Guide, Management Assertion Letter, CUEC Guide with 10 templated controls, and Common Findings & Remediation tables.
Walk into the audit prepared, not scramblingAdditional TSC Policies
Availability (A1), Confidentiality (C1), Processing Integrity (PI1), Privacy (P1–P8), Data Retention, and Secure SDLC — extending beyond Security to all five categories.
Full TSC coverage when your scope requires itExecutive Materials
SOC 2 Program Charter with budget template, Quarterly Security Report for progress tracking, Board Governance Brief for executive oversight.
Give your board the timeline and metrics they're asking forImplementation Roadmap
5-phase plan (Assess → Document → Implement → Test → Audit) with Customisation Guide and placeholder registry.
A structured path from "we need SOC 2" to audit-readyWhat these documents actually look like
Every Excel workbook includes formulas, conditional formatting, dropdown validation, and sample data. Control narratives use the language auditors expect. The System Description follows AICPA structure with guidance notes — your team fills in environment-specific details rather than inventing the format.
69 documents structured around the framework your auditor evaluates
System Description · Control Narratives · Evidence Workbooks · Policies · Procedures · Auditor Prep
When someone asks, here’s what happens
Customer asks for your SOC 2 report
You respond with "SOC 2 readiness in progress" and mean it — with a System Description, control matrix, and evidence workbook to back it up. No stalling, no lost deal.
Auditor evaluates your documentation
They see documentation structured around the Trust Services Criteria they evaluate. Control narratives in the language they expect. Evidence mapped to specific controls. No follow-up questions about document structure.
Board asks for a SOC 2 timeline
You present the 5-phase Implementation Roadmap with the Program Charter. Budget, milestones, and progress metrics — the structured answer that builds confidence.
You already have NIST or ISO documentation
The TSC-to-Framework Crosswalk shows exactly which requirements you already satisfy. Fill in the SOC 2-specific gaps — system description, control narratives, evidence workbooks — without duplicating work.
The cost comparison
Who this is for
✓ Right fit
B2B SaaS companies, startups scaling into enterprise sales, and IT teams tasked with SOC 2 without a dedicated GRC function. MSPs and vCISOs who need repeatable SOC 2 documentation baselines for multiple clients.
✗ Not the right fit
Enterprises with existing compliance platforms and dedicated audit teams. Companies that only need a basic security documentation foundation — the Security Program Foundation Toolkit covers that at $497.
Common questions
Does this cover SOC 2 Type I and Type II?
Yes. The documentation supports both. Type I evaluates control design at a point in time. Type II evaluates operating effectiveness over a period (typically 6–12 months). The forms and trackers capture the ongoing evidence Type II requires.
Do I still need an auditor?
Yes. SOC 2 reports must be issued by an independent CPA firm. This suite provides the documentation and evidence framework — your auditor evaluates and attests to it. The Auditor Preparation Package helps you prepare for the engagement.
Which Trust Service Categories should I include?
Security (CC1–CC9) is mandatory for every SOC 2 report. Availability, Confidentiality, Processing Integrity, and Privacy are optional depending on your services. The Essentials tier covers Security; the Professional tier extends to all five.
I already have NIST CSF or ISO 27001 documentation. Do I need this?
The TSC-to-Framework Crosswalk shows exactly which existing controls satisfy SOC 2 requirements. The SOC 2-specific documents — system description, control narratives, evidence workbooks — are unique to SOC 2 and not covered by generic NIST or ISO documentation.
What file formats are included?
Policies and procedures are Word (.docx). Control matrices, trackers, and workbooks are Excel (.xlsx). All files use standard fonts and formatting — compatible with Microsoft 365, Google Workspace, and LibreOffice.
Do I get updates if the product is improved?
Yes. If we update this product within 12 months of your purchase — framework changes, new templates, content improvements — you receive the updated files automatically at no additional cost. After 12 months, you keep everything you have permanently. Future updates are available at a renewal discount.
Is AI used in creating these documents?
Ridgeline uses AI tools in the research and drafting process. All documentation is written, reviewed, and validated by a security practitioner to ensure it is operationally sound and aligned with current frameworks.
What if we need help customising it?
Our Implementation Services team will customise the documentation to your environment — technology stack, service scope, regulatory requirements. Suite tier is $5,997, delivered in 1–2 weeks.
How does this compare?
| Capability | Free templates | SOC 2 Readiness Suite | GRC platform ($15K+/yr) |
|---|---|---|---|
| Framework-aligned documentation | Some | ✓ Full coverage | ✓ |
| Editable Word/Excel files | ✓ | ✓ | ✗ Locked in platform |
| Interactive browser app | ✗ | ✓ Included | ✓ |
| One-time cost | ✓ Free | ✓ $997 | ✗ Annual subscription |
| Implementation time | Weeks | ✓ Hours | Months |
| Audit-ready formatting | ✗ Inconsistent | ✓ Professional | ✓ |
Get notified about updates to this toolkit
Get notified when we launch new toolkits
Product launches only · No spam · Unsubscribe anytime
Implementation Services
Need this customised to your organisation?
We'll customise any product to your organisation and deliver in 1–2 weeks. Fixed price, fully async. You review it, your team runs it.
Foundation $1,997 · Toolkit $2,997 · Suite $5,997 · Program $8,997