Zero Trust Implementation Toolkit
26 documents, 10 Excel engines, and a 13-script automation pipeline covering all 5 CISA Zero Trust pillars — from board-level policy to platform-specific implementation across Entra ID, Google Workspace, and AWS.
Zero Trust Implementation Toolkit
Everyone agrees on Zero Trust. Nobody tells you how to implement it.
NIST SP 800-207 defines the architecture. The CISA Maturity Model maps the journey. Your board has approved the strategy. But between reading the framework and running a Zero Trust program, there’s a gap nobody fills — the policies, standards, platform-specific checklists, tracking workbooks, and automation that turn principles into implementation.
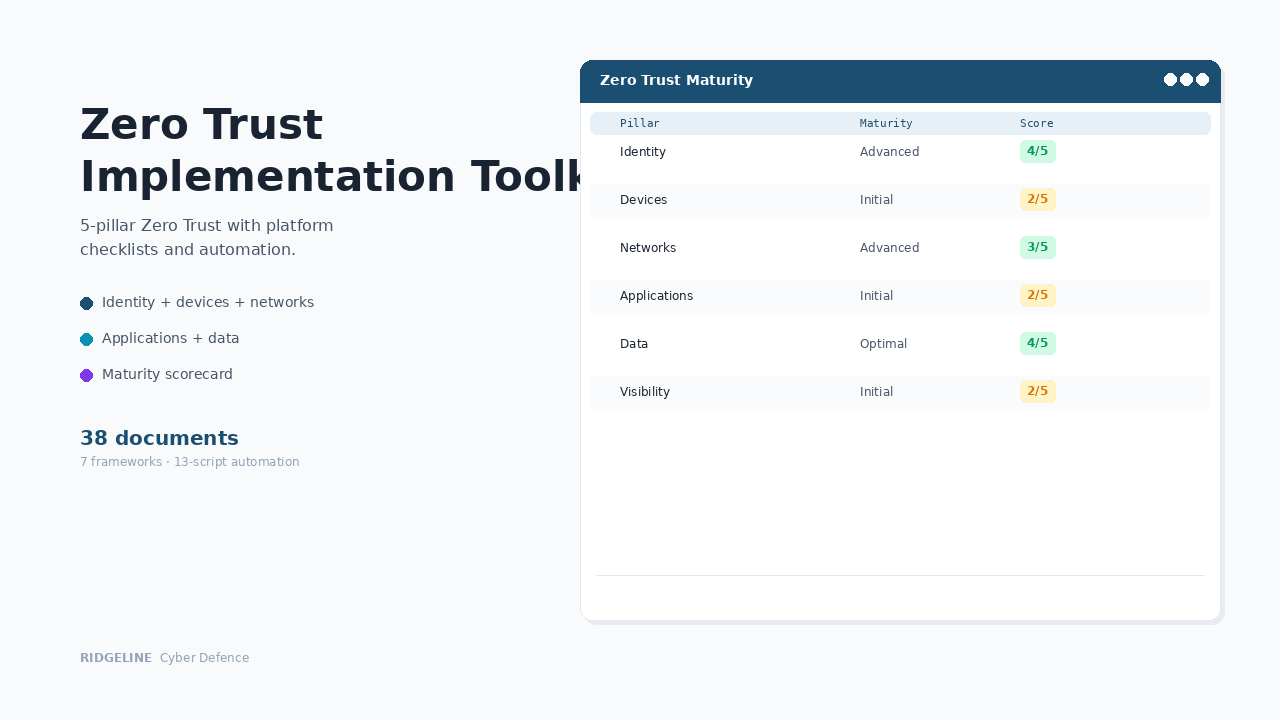
This toolkit delivers 38 operational deliverables across all 5 CISA pillars, with platform-specific checklists for your actual platforms and a 13-script automation pipeline that replaces weeks of manual data gathering.
What’s inside
Govern and measure
Board-level governance and the maturity tracking your auditor and board expect.
Zero Trust Security Policy
Board-level policy covering all five CISA pillars — ZTA principles, governance structure, monitoring requirements, exception management, enforcement.
The governance foundation your board approvesMaturity Scorecard
Excel workbook scoring all five CISA ZTMM pillars across four maturity levels (Traditional → Optimal) with evidence logging and trend tracking.
Show the board a clear trajectory, not qualitative statementsFramework Cross-Mapping
Every toolkit requirement mapped across eight compliance frameworks: NIST 800-207, CISA ZTMM, ISO 27001, NIST CSF 2.0, CIS v8, SOC 2, CMMC 2.0.
One implementation satisfies multiple audits simultaneouslyZero Trust Risk Assessment
6-tab Excel workbook with 31 pre-populated risks across all five pillars. Auto-calculated scoring, treatment plans, heat map, and dashboard.
Risk-driven implementation, not checkbox complianceImplement across all 5 pillars
Platform-specific standards, workbooks, and checklists — not generic guidance.
Identity Pillar — 11 files
Authentication standard, RBAC matrix (162 SoD conflict pairs), privileged access inventory, access review workbook, PAM procedure, platform checklists for Entra ID (~55 controls), Google Workspace (~35), AWS (~40).
Not "configure MFA" — the actual steps in your platformDevices Pillar — 2 files
Device trust standard with CIS benchmarks, trust scoring (0–100), platform configs for Intune, Jamf, Chrome Enterprise, AWS Systems Manager. 6-tab compliance inventory.
Trusted devices only — with the scoring to prove itNetworks & Applications — 4 files
Network segmentation standard with 5 mandatory zones, firewall rules, VPN-to-ZTNA migration. Application security standard with SDLC, API security, SaaS governance. Tracking inventories for both.
Micro-segmentation documented and trackedData Pillar — 2 files
Four classification tiers, encryption standards, DLP enforcement, platform config for Microsoft Purview, Google DLP, AWS Macie. Data stores register with retention schedules.
Know where your data is and how it's protectedAutomate and verify
A 13-script pipeline that replaces weeks of manual data gathering.
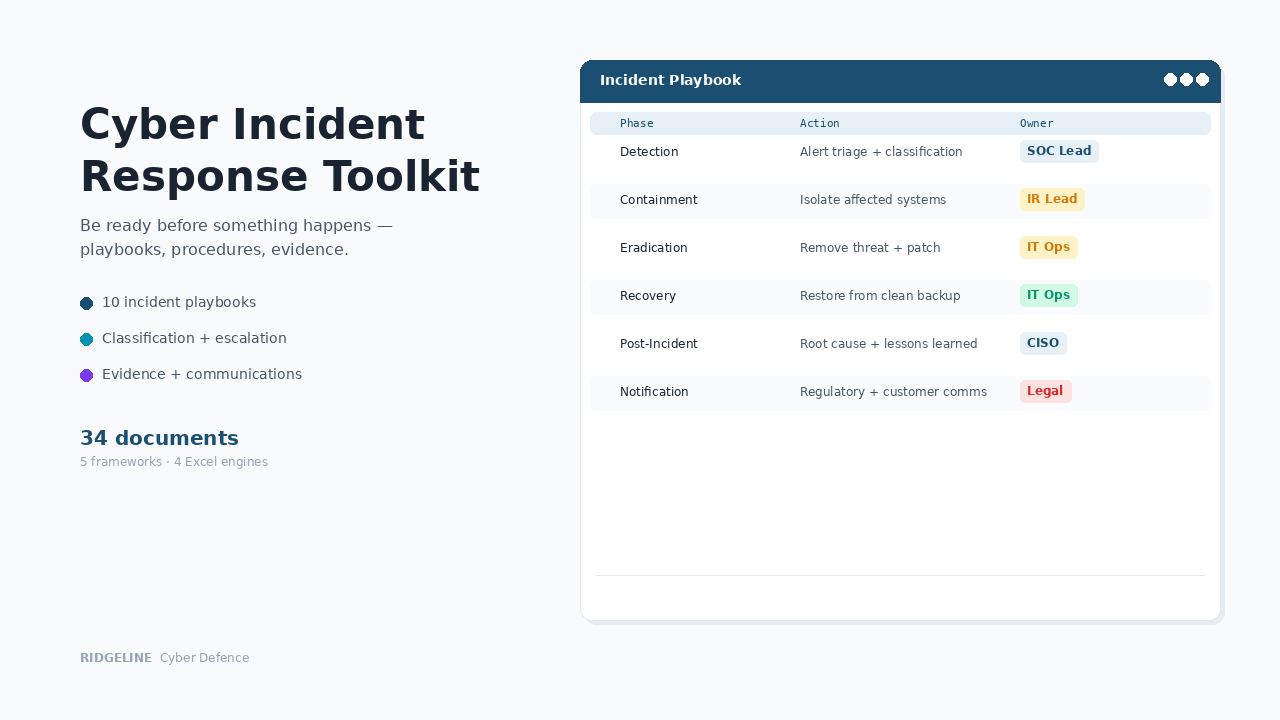
Platform Collectors
Four scripts pulling identity data from Entra ID, Active Directory, AWS IAM, and Google Workspace. Read-only permissions. Auto-normalises cross-platform data.
Minutes instead of weeks for quarterly data collectionAssessment Engine
Browser-based interactive engine scoring Zero Trust maturity across all five CISA ZTMM pillars from collected data.
Maturity assessment from real data, not self-reported questionnairesRemediation & Evidence
Generates platform-specific fix scripts with dry-run modes. Verifies controls post-remediation with PASS/FAIL/WARN mapped to 5 frameworks.
Fix the gaps, then prove you fixed themExecutive Report Generator
Produces branded DOCX executive summary with maturity radar, findings, remediation priorities, evidence summary, and framework compliance status.
Board-ready report from one commandWhat these documents actually look like
Platform checklists contain exact navigation paths, setting names, and configuration values — not generic guidance. Excel workbooks include formulas, conditional formatting, and auto-calculated scoring. The automation pipeline runs end-to-end with one command and produces a branded executive report.
All 5 CISA pillars. Your actual platforms. One system.
Identity · Devices · Networks · Applications · Data · Automation · Compliance
When someone asks, here’s what happens
Board asks "where are we on Zero Trust?"
You present the Maturity Scorecard with quarterly progression across all five pillars. Visual trajectory from Traditional to target state. Data-driven, not qualitative.
Auditor asks about identity controls
You show the RBAC matrix with SoD conflict detection, the access review workbook with audit trails, and the platform checklists with verified configuration. Evidence mapped to ISO 27001, SOC 2, and CMMC simultaneously.
Quarterly compliance evidence collection
You run the automation pipeline. Four collectors, normalisation, assessment, and report generation — minutes instead of the 2–3 weeks it takes manually.
The cost comparison
Who this is for
✓ Right fit
IT managers and security engineers implementing Zero Trust with Microsoft 365, Google Workspace, or AWS. CISOs who need board-level governance and maturity tracking. Compliance teams needing audit evidence mapped across multiple frameworks.
✗ Not the right fit
Enterprises with dedicated Zero Trust platforms and implementation teams. Organisations looking for technology solutions — this provides the operational documentation and automation layer, not the security products themselves.
Common questions
Do I need the automation scripts to use this?
No. Every workbook works in fully manual mode. The automation scripts accelerate data collection and reduce manual effort, but the documents stand alone without them.
How does this differ from free Zero Trust frameworks?
NIST SP 800-207 and the CISA ZTMM tell you what to do. This toolkit tells you how — with the actual policies, standards, workbooks, platform-specific checklists, and automation that verifies your controls. It's the operational layer between framework and platform.
What platforms do the automation scripts support?
The four collectors support Microsoft Entra ID, on-premises Active Directory, AWS IAM, and Google Workspace. All use read-only permissions. Remediation scripts require explicit execution.
What file formats are included?
Word (.docx) for policies, standards, procedures, checklists, and guides. Excel (.xlsx) for all operational workbooks. Python and PowerShell scripts for automation. HTML applications for assessment engine and command centre.
Do I get updates if the product is improved?
Yes. If we update this product within 12 months of your purchase — framework changes, new templates, content improvements — you receive the updated files automatically at no additional cost. After 12 months, you keep everything you have permanently. Future updates are available at a renewal discount.
Is AI used in creating these documents?
Ridgeline uses AI tools in the research and drafting process. All documentation is written, reviewed, and validated by a security practitioner to ensure it is operationally sound and aligned with current frameworks.
What if we need help customising it?
Our Implementation Services team will configure the workbooks, customise platform checklists, and run the initial maturity assessment. Toolkit tier is $2,997, delivered in 1–2 weeks.
How does this compare?
| Capability | Free templates | Zero Trust Implementation Toolkit | GRC platform ($15K+/yr) |
|---|---|---|---|
| Framework-aligned documentation | Some | ✓ Full coverage | ✓ |
| Editable Word/Excel files | ✓ | ✓ | ✗ Locked in platform |
| Interactive browser app | ✗ | ✓ Included | ✓ |
| One-time cost | ✓ Free | ✓ $797 | ✗ Annual subscription |
| Implementation time | Weeks | ✓ Hours | Months |
| Audit-ready formatting | ✗ Inconsistent | ✓ Professional | ✓ |
Get notified about updates to this toolkit
Get notified when we launch new toolkits
Product launches only · No spam · Unsubscribe anytime
Implementation Services
Need this customised to your organisation?
We'll customise any product to your organisation and deliver in 1–2 weeks. Fixed price, fully async. You review it, your team runs it.
Foundation $1,997 · Toolkit $2,997 · Suite $5,997 · Program $8,997